AI Security For Your Agents
Move Fast. Build Agentic. Stay Secure.
Your Security Stack Wasn’t Built for This
Your agents call APIs, chain tools, and act on behalf of users. Here’s what your existing tools miss.
Every new agent deployment widens the gap between what’s in production, and what your team can see. Traditional tools can’t reason about agent behavior.
Prompt injection, tool misuse, data exfiltration through agent chains, your scanners and firewalls were designed for a world where software does what it’s told.
Agents run and adapt in real time. Behavior changes as models update and tools are connected. Point-in-time reviews are outdated before they’re finished.
Ask "Am I Ready to Launch?" Get an Answer You Can Act On.
Connect your AI agents, AI-native apps, Claude, Lovable, OpenClaw or a URL. Trent gives you a security posture snapshot: how many critical issues you have, what to fix first, and how many remediation tasks remain. Each time you run an assessment, the picture gets sharper.
See how the agents work →

Secure Your Ongoing Agent Development
An ever-evolving blueprint of your application’s threat landscape, built into every commit, update, and design iteration.
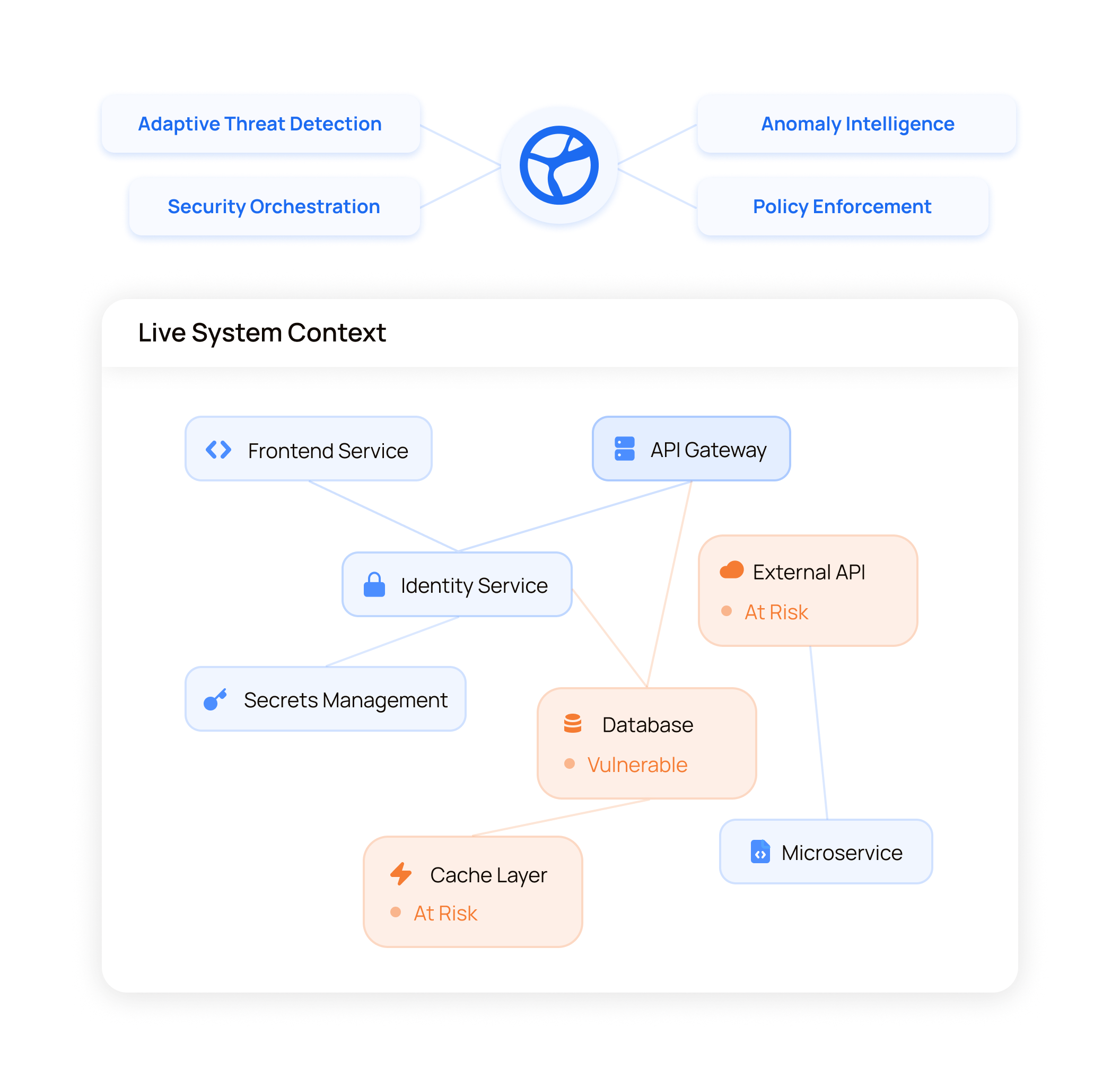
Actively interprets your application’s architecture, objectives, and operational context the way a world-class security engineer would, not through static rules or checkbox scans.

Anticipates threats, simulates potential attack paths, and guides you toward secure design decisions while you build.

A Prioritized Plan, Not a List of Alerts.
Other tools give you a wall of CVEs. Trent gives you a remediation plan, 12 actionable controls, classified by severity, with clear instructions your team can execute immediately. Critical issues first. Low-risk noise filtered out.

Review the Plan. Click Execute. Track Progress.
Trent builds the fix plan. You review it and approve. Trent applies the fixes, directly through Claude Code, Lovable, or your CI/CD workflow. Then it tracks which tasks are completed, which are in progress, and what’s left. Every re-scan updates the picture.

Design Your Agents Securely From Day One
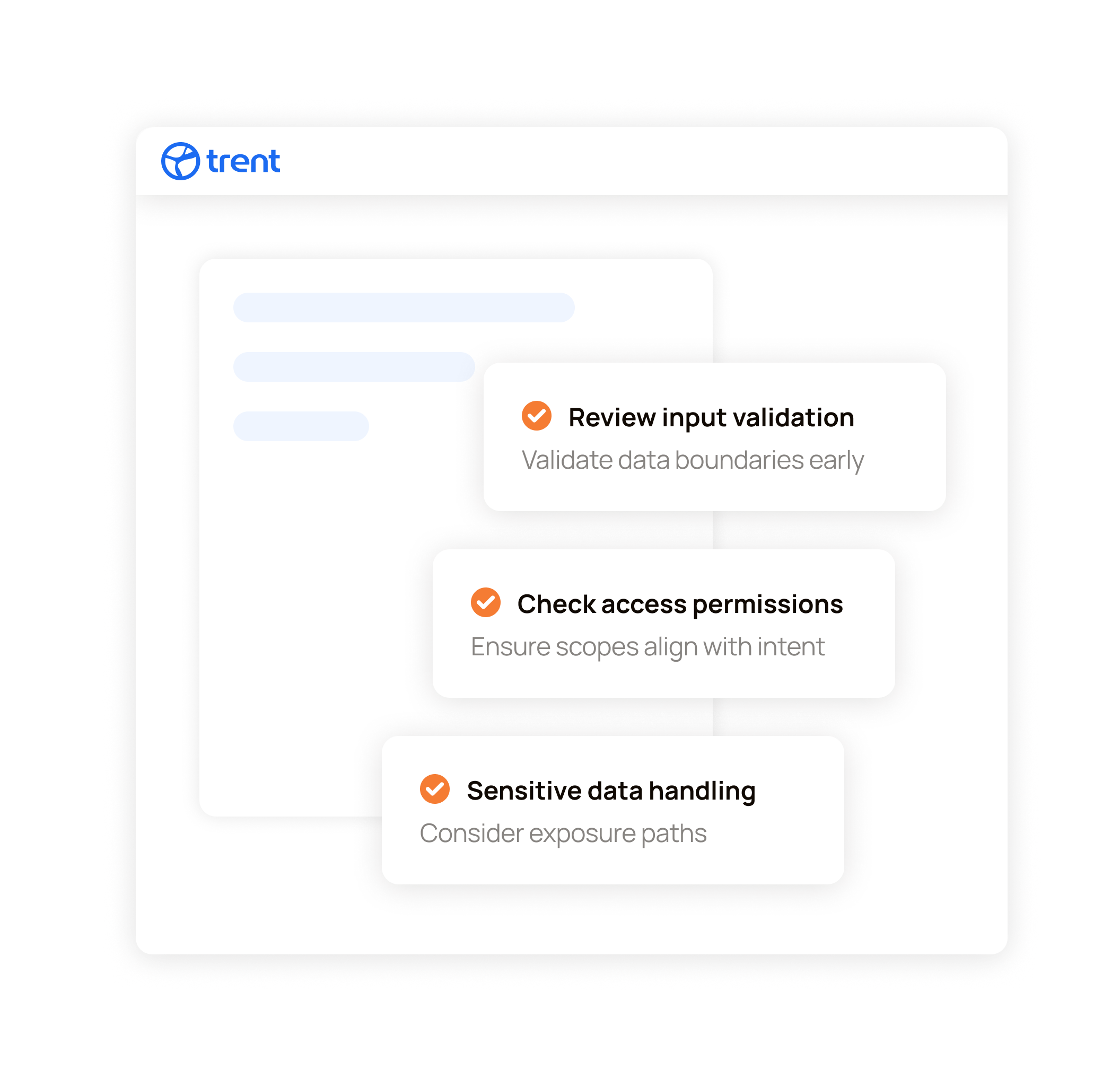
A Security Engineer at your side, asking the right questions, guiding your design thinking, and helping you anticipate risks before they appear.

A conversational design process that helps you architect and shape your application securely from the start.

Continuous, context-aware guidance, so you can be certain your application remains secure from the first design sketch to the final release.
The Threats Your Existing Tools Miss
Why Not Your Existing Tools?
Your team already runs security tools. Here’s why they’re not enough for what you’re building now.
Trent is the right choice when you value:
- Security that learns and compounds with every cycle
- Coverage across your entire agent stack, code, agents, infrastructure, and workflows
- Continuous assessment, not point-in-time reports
- Specialized agents that scan, judge, mitigate, and evaluate, not generic tools repurposed for agentic systems
Find code-level issues known vulnerabilities, insecure dependencies, flagged patterns. They can’t reason about agent behavior, prompt-driven logic, or the risks created when AI agents call APIs, chain tools, and act on behalf of users. Different threat model entirely.
Point-in-time engagement. Weeks of consultant time. A PDF report that’s outdated before you read it. Your agents change behavior every time a model updates or a tool is connected. You need continuous assessment, not a quarterly exercise.
Secure your cloud infrastructure, IAM, network, storage. They don’t see inside your AI application layer: prompt safety, agent permissions, tool misuse, data exfiltration through agent chains. Cloud posture is necessary but not sufficient.
Build Agentic. Stay Secure.
Connect your environment. Your security compounds from day one.





